Source: PhysOrg.com
By analyzing network traffic going to suspicious domains, security administrators could detect malware infections weeks or even months before they’re able to capture a sample of the invading malware, a new study suggests. The findings point toward the need for new malware-independent detection strategies that will give network defenders the ability to identify network security breaches in a more timely manner.
The strategy would take advantage of the fact that malware invaders need to communicate with their command and control computers, creating network traffic that can be detected and analyzed. Having an earlier warning of developing malware infections could enable quicker responses and potentially reduce the impact of attacks, the study’s researchers say.
“Our study shows that by the time you find the malware, it’s already too late because the network communications and domain names used by the malware were active weeks or even months before the actual malware was discovered,” said Manos Antonakakis, an assistant professor in the School of Electrical and Computer Engineering at the Georgia Institute of Technology. “These findings show that we need to fundamentally change the way we think about network defense.”
Traditional defenses depend on the detection of malware in a network. While analyzing malware samples can identify suspicious domains and help attribute network attacks to their sources, relying on samples to drive defensive actions gives malicious actors a critical time advantage to gather information and cause damage. “What we need to do is minimize the amount of time between the compromise and the detection event,” Antonakakis added.
The research, which will be presented May 24 at the 38th IEEE Security and Privacy Symposium in San Jose, California, was supported by the U.S. Department of Commerce, the National Science Foundation, the Air Force Research Laboratory and the Defense Advanced Research Projects Agency. The project was done in collaboration with EURECOM in France and the IMDEA Software Institute in Spain – whose work was supported by the regional government of Madrid and the government of Spain.
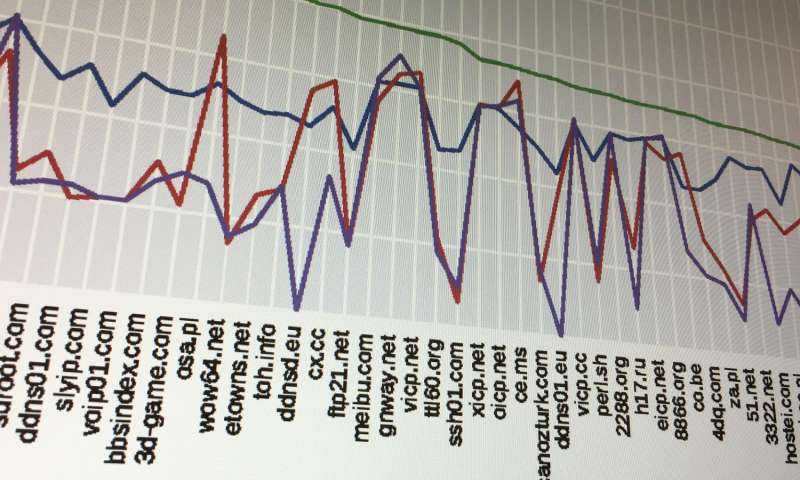
In the study, Antonakakis, Graduate Research Assistant Chaz Lever and colleagues analyzed more than five billion network events from nearly five years of network traffic carried by a major U.S. internet service provider (ISP). They also studied domain name server (DNS) requests made by nearly 27 million malware samples, and examined the timing for the re-registration of expired domains – which often provide the launch sites for malware attacks.
Click here to read more